

SQLite Forensics Explained
SQLite forensics explained in simple terms. Learn how SQLite databases store data, where evidence is hidden, and why it matters in digital investigations.
Enhance your toolkit with clearer, more precise forensic analysis. Designed to complement your trusted platforms, our solutions help you work sharper and with greater precision.
Learn how to master comprehensive digital forensics workflows through immersive, hands-on training. Confidently apply your skills in real investigations.
Targeted micro-learning modules to help you rapidly address critical challenges, strengthen expertise, and stay fully up to date.
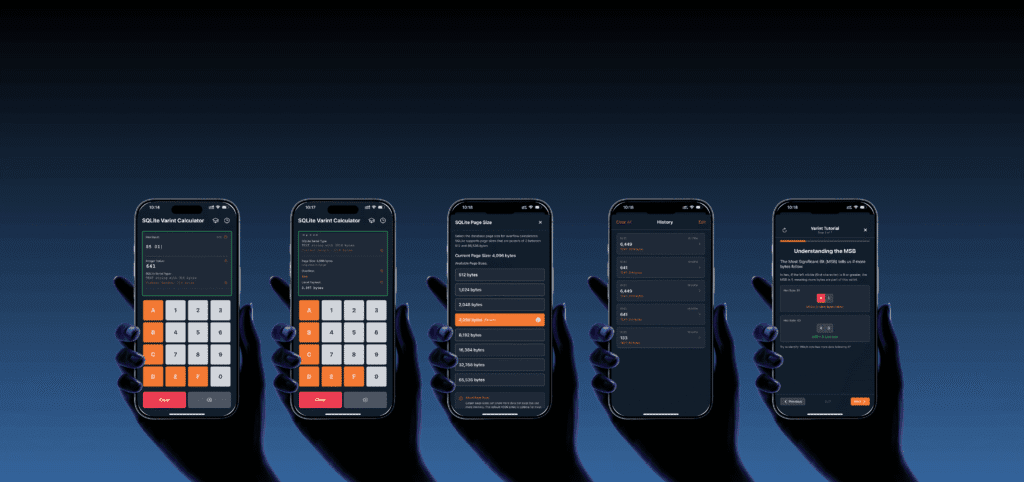
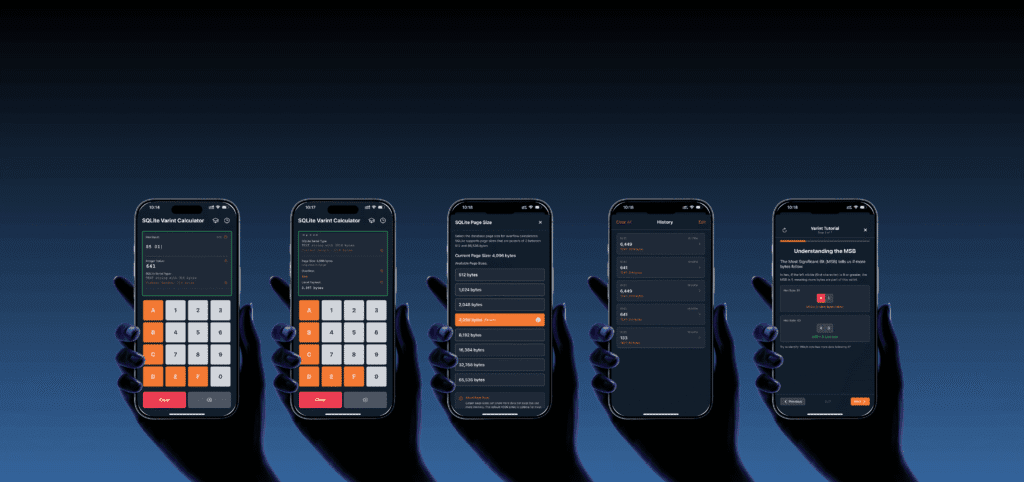
Instantly decode variable-length integers from SQLite databases, protobuf messages, and app data structures. This utility converts hex values to decimal in seconds, perfect for analyzing WhatsApp databases, custom app formats, and messaging data without requiring custom scripts.
ED SQLite Visualizer transforms how you analyze mobile databases. Trace deleted records frame by frame. Map complex schema relationships visually. Recover evidence from WAL files and unallocated space through an intuitive interface designed for modern investigations.
Transform iOS backup data into organized, navigable file structures. This free Windows tool extracts and normalizes iTunes backup content, complete with hash verification and device metadata. Access your backup data through a clear, logical file system ready for efficient analysis and reporting.
Learn to extract deleted or uncommitted data from WAL and SHM, reconstruct timelines, and uncover hidden app activity your tools can’t show.
Learn to manually decode pages, recover deleted records, and confidently validate your findings, perfect when you need precise, court-ready evidence.
Start strong with the essentials. Learn how to collect, examine, and explain digital evidence. From data acquisition to reporting, build practical skills through real cases and guided labs. Built for those starting out or refreshing the basics.
Become an expert in mobile forensics, from acquisition to reporting. Built for real cases, updated for today’s Android and iOS challenges. Gain skills that go beyond tool output.
Explore SQLite databases in depth, the hidden layer beneath mobile apps and operating systems. Learn how to extract, decode, and interpret data to uncover user activity and forensic artifacts.
Dig deep into unsupported apps with hands-on SQLite analysis. Use Python to script, automate, and extract what tools miss. Gain a technical edge for advanced mobile forensics.


Learn when it works for you. 24/7 access to real-case modules. Pause, replay, and apply at your own pace.


Join live sessions from anywhere. Ask questions, try out techniques, and learn by doing. All the energy of the classroom, without the commute.


Learn in person from expert forensic practitioners through hands-on labs designed to build deep, practical skills.
This free guide provides a practical walkthrough of GPT-partitioned disks, covering the Protective MBR, GPT Header, and Partition Entry Array. It’s designed to help forensic professionals understand disk structures, recover data, and validate evidence.
This guide provides a practical walkthrough for forensic analysts dealing with encrypted Apple Notes in iOS 16.x. It focuses on identifying and decrypting locked notes stored in the NoteStore.sqlite database extracted from iOS backups.
Very good course! Incredibly good teacher and I think that distance learning works at least as well as in the classroom! Thanks again James! Great balance between technical depth and hands-on labs. I liked that we didn’t just rely on tools, but looked under the hood and made sense of the data. It’s definitely helped me write clearer reports and explain findings to investigators.
Best course I have ever taken. I really enjoyed the week, learned a ton, and everything was clear and easy to keep up with. The labs felt real and made sense, even without loads of experience. The instructor explained things so clearly and made it all feel manageable. I would absolutely recommend it to anyone working with mobile forensics.
After decades of solving cases, testifying in court, and training forensic teams around the world, James Eichbaum founded Elusive Data in early 2024.
Well known in the digital forensics community from his former roles as an investigator, Global Training Manager, and instructor for some of the leading names in the industry, James started the company with a clear idea: training should be more hands-on, immersive, and reflect the real challenges of daily investigations. It should also be more accessible, giving investigators faster access to the knowledge they need to act quickly, make sense of complex data, and solve cases without delay.
Today, Elusive Data helps professionals around the world learn through immersive, hands-on training. Courses include interactive labs, CTF challenges, and practical exercises built around real case data. Training is available on-demand, live online, and on-site.
Along the way, it became clear that some of the biggest challenges investigators face are more than just knowledge.
Gaps between what tools show and what investigators need to understand kept slowing work down.
That’s why Elusive Data also develops focused forensic tools: practical utilities built directly from training, casework, and day-to-day investigative needs — designed to remove friction, provide clarity, and support defensible analysis.
Elusive Data also supports active investigations through expert consulting and forensic services, for a field that never stands still.


Get help uncovering and explaining digital evidence. We deliver clear, reliable results for investigations, legal cases, and internal reviews.


Build stronger forensic capabilities with expert guidance. From setting up labs to improving workflows. We help you work smarter, faster.
Our courses sharpen the way you investigate digital and mobile evidence. You learn full workflows that go beyond tool buttons — working with raw data, decoding app artifacts, and practicing authentic case scenarios. Labs and CTF challenges give you confidence to handle live investigations under real conditions.
We offer four certification programs: Introduction to Digital Forensics, Mobile Device Forensics, SQLite Forensics, and Python for Mobile Forensics. Each program builds practical skills that complement your existing tools and help you see more, find more, and deliver precise results that hold up in reports and courtrooms.
Yes. All training has been fully updated to match the current forensic landscape. That includes support for modern iOS and Android environments, new app structures, updated CTF scenarios, and deep dives into advanced topics like SQLite freelist recovery and manual decoding of WAL/SHM files.
Our tools are built to meet today’s forensic challenges. They don’t replace your trusted platforms — they extend them. Some give you quick answers when time is short, others open up evidence in ways no other tool can.
VarInt Calculator – Decode variable-length integers instantly from SQLite databases. No scripts, no guesswork. Just clear values when you need them.
Backup2FS – Transform iOS backups into structured, navigable file systems with hashes and metadata preserved. From confusion to clarity in one step.
SQLite Visualizer – A full forensic suite for database analysis. Visualize structures, follow deleted records across time, and recover hidden evidence from WAL, freelists, and unallocated space. Built from years of training and investigations, it reveals what standard tools often miss.
Together, these tools give you sharper insight, clearer reporting, and results that hold up in real investigations.
We built ED SQLite Visualizer because we needed a clearer way to investigate SQLite in real cases. Again and again, the same questions appeared: What was deleted — and when? Where did this record come from? How can I explain this in a report?
The tool fills that gap. It shows deleted records frame by frame, maps schema relationships as a visual canvas, and recovers data from WAL, freelists, and unallocated space. Born from casework and refined in hands-on labs, ED SQLite Visualizer makes forensic analysis faster, clearer, and easier to explain — especially when time is short.
ED SQLite Visualizer is not another database viewer — it’s a new way to explore forensic questions. Instead of rows and hex, you see the story inside the database.
Key capabilities include:
WAL Timeline Viewer – Watch database history unfold, record by record.
Smart Canvas Navigation – Visualize entire schemas as interactive maps.
Integrated Hex & Structure View – Explore freelists, overflow chains, and pages without losing context.
One-Click Recovery – Extract deleted data from WAL, freelists, and unallocated space.
Built-in Evidence Tools – Protect source data, verify with SHA1, and generate reports.
Shaped by real-world challenges and used in our certified SQLite training, ED SQLite Visualizer gives investigators a faster, more connected way to see what’s really in the data.
You can choose the format that fits your goals and schedule:
Micro-Courses: Short, focused live sessions (60–90 minutes) on specific topics like GPT, SQLite, and encrypted apps — ideal for fast, practical learning.
On-Demand Courses: Access certified, self-paced training 24/7. Replay labs, follow guided exercises, and apply techniques at your own speed.
Live Online Courses: Join expert-led classes in real time. Participate in case discussions, ask questions, and complete labs with instructor feedback.
Classroom Training: Learn face-to-face through immersive sessions and hands-on labs led by experienced digital forensics professionals.
Yes. All full-length courses include a verified certificate of completion and CPE credits, recognized by many professional bodies.
Our training supports all experience levels. You can start with foundational skills like acquisition and validation, or deepen your expertise with advanced techniques such as parsing app databases and scripting with Python for forensic automation.
No. They are built to simplify complex forensic tasks. Whether you’re decoding VarInts, navigating an iOS backup, or exploring database internals, the goal is to make the process faster, clearer, and easier to explain.
When you purchase SQLite Visualizer, a one-hour training session is included to help you get started right away. For those who want to go deeper, in-depth courses using the tool will be available across all our training formats — from live online to on-demand modules and classroom sessions.


SQLite forensics explained in simple terms. Learn how SQLite databases store data, where evidence is hidden, and why it matters in digital investigations.


Protobuf varints are not SQLite varints. Learn how to parse Protocol Buffer data from Apple Notes and mobile forensic artifacts, decode LEB128 varints step by step, and build a Python decoder with bitwise operations. Includes a hands-on XOR decryption challenge.


Making digital forensics training more accessible Elusive Data was founded in early 2024 with a clear purpose: to make advanced digital forensics training more accessible,
PRESS RELEASE Stockholm, Sweden – December 9, 2025 Elusive Data has officially released SQLiteVisualizer™, a next-generation forensicplatform that gives investigators unprecedented insight into how mobile
Small time-savers can make a big difference in mobile forensics.
That’s why VarInt Calculator is now available as a dedicated iOS app—bringing fast VarInt decoding and clear SQLite insights straight to your iPhone or iPad.
Something new is coming to mobile forensics At Elusive Data, our mission has always been clear: to help forensic professionals work faster, more accurately, and


New course out now: Gain control over app data like never before. Learn to uncover, validate, and defend hidden evidence — no waiting, no travel.
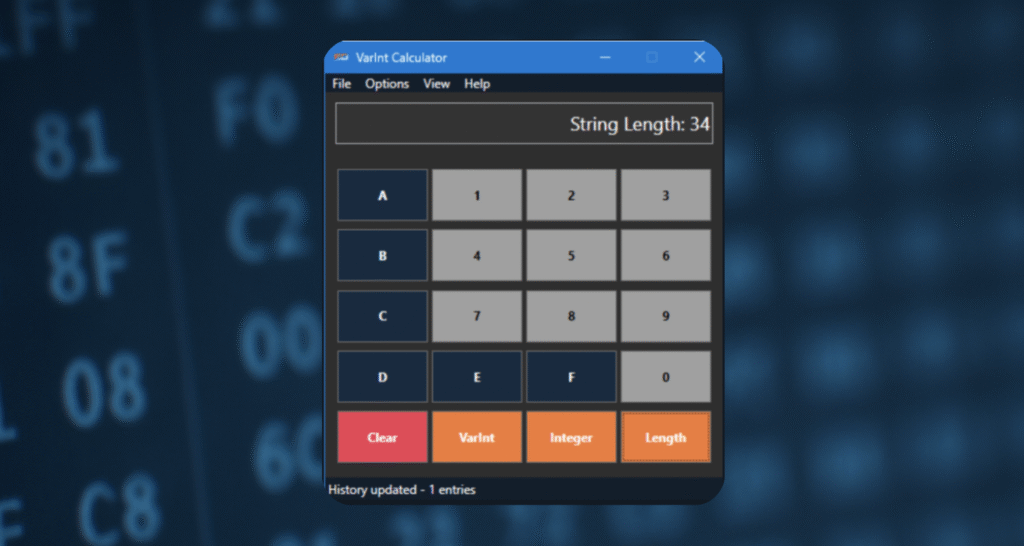
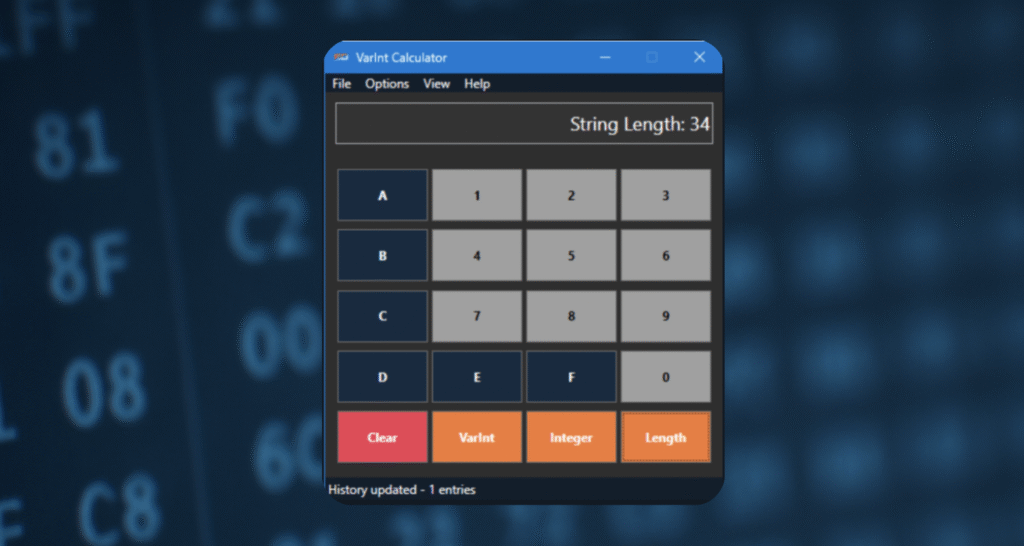
Instantly decode VarInts from mobile app databases with Elusive Data’s free forensic tool. Convert hex, binary, and decimal values for faster, more accurate investigations.


Discover Backup2FS, a free tool from Elusive Data that simplifies iOS backup analysis by normalizing backups into an easy-to-navigate file system.
Thank you for a great course! I finally get how to work with unsupported apps. That clicked during this course. I’ve done a few trainings before, but this one stood out because it was actually useful right away. The instructor explained how app data is stored in a way that made sense, and I really appreciated all the real examples. I’ve already used a few techniques in a current case.